CMMC Consulting Services
Assess, Plan and Prepare for CMMC Certification
Our CMMC Consulting Services Team brings real-world cybersecurity and risk assessment experience to guide organizations through CMMC readiness and audit preparation.
What is CMMC Certification?

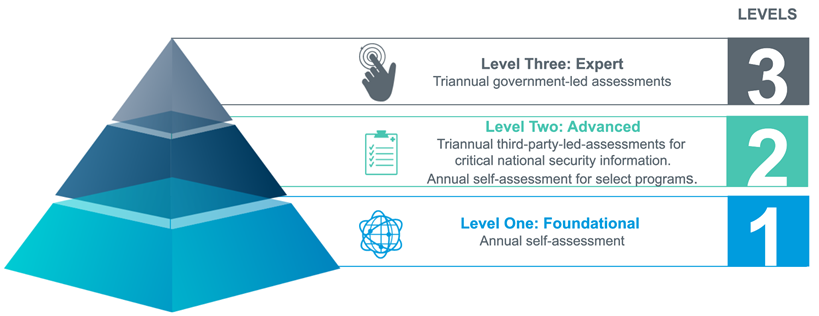
The Cybersecurity Maturity Model Certification (CMMC) is the Department of Defense’s framework for improving and assessing cybersecurity practices across the Defense Industrial Base (DIB). Any organization handling federal contract information (FCI) or controlled unclassified information (CUI) must demonstrate appropriate cybersecurity practices under the Department of Defense’s CMMC framework.
CMMC Compliance Consulting and Readiness Support
As a Registered Practitioner Organization (RPO), Withum is recognized by The Cyber AB to guide organizations of all sizes through CMMC readiness and certification preparation. With extensive expertise in cybersecurity, risk management and defense contracting, our CMMC consultants help organizations navigate the complexities of CMMC certification requirements and formulate a tailored approach to CMMC audit preparation appropriate to the organization’s required Maturity Level (e.g., ML1, ML3, etc.).
Core CMMC Consulting Services
Our CMMC compliance consulting services support organizations at every stage of CMMC readiness, from initial assessment through audit preparation and certification support.
Evaluate your current cybersecurity maturity and identify gaps against CMMC requirements.
Develop an actionable roadmap to address identified gaps efficiently and align with your target maturity level.
Create or refine security documentation to meet audit expectations.
Support internal teams through documentation review, control validation, and pre-assessment coaching.
Connect with Our Leaders
Contact Us
For more information or to discuss your business needs, please connect with a member of our team.


