Revolutionizing Collaboration With Identity Security: Your Journey to Microsoft 365 and Google Workspace Integration
This blog post unveils my plan to optimize collaboration and identity security between users of Microsoft 365 and Google Workspace. While a single environment ultimately would make collaboration and management easier, it is sometimes impossible due to significantly large migration effort/user impact or existing licensing commitments or other complexities.
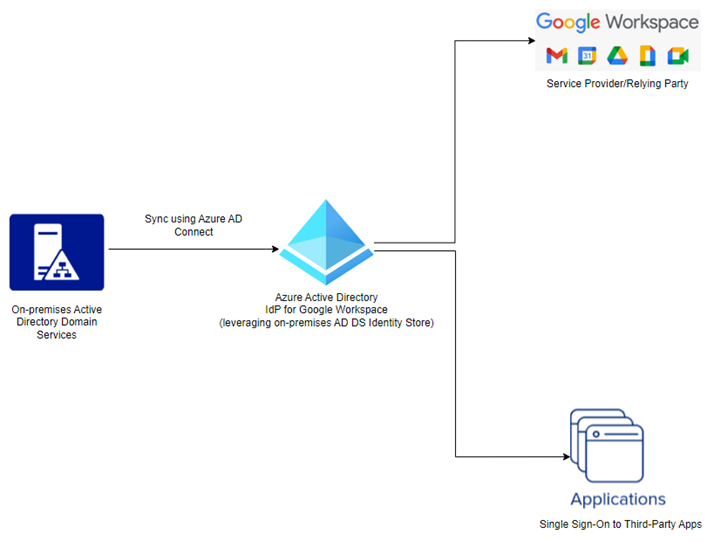
The primary objectives of this integration encompass removing the complexities of Okta and its significant licensing cost, eliminating duplicate accounts, establishing a coexistence between platforms, preserving user UPNs, automating lifecycle management and enhancing the overall security posture. In this article, I detail how I leveraged Entra ID (Azure AD) as the Identity Provider (IdP) and Google Workspace as the Service Provider (SP), ensuring a seamless integration to maximize productivity and user satisfaction. For more on this client and project, please click here.
Goals and Pain Points
My client embarked on this transformative journey with clear objectives aimed at resolving existing pain points:
- Eliminate Duplicate Accounts: Duplicate accounts not only create confusion but also introduce IT management overhead. By streamlining and consolidating user accounts and credentials, we aimed to simplify operations and reduce potential issues associated with duplicate accounts.
- Establish Coexistence Capabilities: Collaborative capabilities for the Global Address List and calendars were a priority. We sought to create an environment where users could seamlessly collaborate, irrespective of their chosen productivity suite, be it Microsoft 365 or Google Workspace.
- Preserve User UPNs: Maintaining User Principal Names (UPNs), or email addresses, across Entra ID and Google was critical to minimizing any disruption for users. This strategic decision ensures users can continue their work unhindered.
- Implement Automated Lifecycle Management: Enhancing security and reducing IT overhead was another pivotal objective. Our plan included the automation of lifecycle management between Entra ID and Google, a significant step toward bolstering the security posture.
- Replace Okta with Entra ID: By leveraging Entra ID’s native capabilities, encompassing Single Sign-On (SSO), Conditional Access and Identity Provider (IdP) functions, we aimed to reduce costs and simplify IT management for our client. This consolidation brings these essential functions under the Entra ID umbrella, eliminating the need for separate systems like Okta.
Ready to Streamline Your Identity Management?
Learn how you can get started with our Okta to Microsoft Entra migration offer in the Microsoft marketplace!
Scope and Tasks
To achieve these objectives, a comprehensive set of tasks was outlined:
- Identity Integration:
- Utilizing Entra ID as the Identity Provider (IdP) and Google Workspace as the Service Provider (SP).
- Synchronizing on-premises Active Directory identities with Entra ID.
- Enabling Free/Busy Calendar coexistence using Google Calendar Interop functionality.
- Creating a unified corporate directory that encompasses users from both platforms.
- Facilitating seamless collaboration and integration for document sharing through OneDrive, SharePoint, Teams and Google Workspace.
- Email Coexistence:
- Establishing a shared domain name across Entra ID/Office 365 and Google.
- Allowing users to log in using their Google email domain name in Entra ID IdP.
- Configuring mail flow to ensure seamless routing between Office 365 and Google for users with mailboxes in Google.
- Setting up an internal relay for the Google domain(s) in Office 365 to prevent mail routing issues.
- Provision User Accounts:
- Exporting Google users and comparing them with existing Entra ID or on-premises AD users.
- Bulk-creating users via CSV file and PowerShell for Google users without corresponding accounts.
- Integrating existing Google staff users into Entra ID or on-premises AD with minimal user impact.
- User Integration Workflow:
- Federating user identities between Google Cloud and Entra ID.
- Synchronizing relevant users and groups from Entra ID to Google Workspace.
- Automating the provisioning and deletion of users between Entra ID and Google.
- Single Sign-On (SSO) and Life Cycle Management (LCM):
- Implementing Entra ID Single Sign-On authentication while leveraging the existing OKTA configuration.
- Enabling automatic provisioning of user identities and roles within Entra ID for supported SaaS applications.
- Cutover Plan:
- Deploying the integration in a phased approach to minimize service disruptions.
- Conducting validation with pilot users to ensure seamless access to both Google and Entra ID environments.
- Migrating SSO applications that support multiple IdPs to Entra ID ahead of time for testing purposes.
Outcome
This blog encapsulates a comprehensive roadmap to address the challenges my client faced, ultimately leading to seamless collaboration between Microsoft 365 and Google Workspace.
By centralizing identity security and management within Entra ID:
- Users within both Entra ID and Google Workspace can now enjoy streamlined access, enhanced security and seamless collaboration across environments, driving productivity and creating an efficient and collaborative work environment.
- Our client successfully reduced costs by decommissioning their Okta environment and licenses while enhancing the user experience.
- The consolidation of management functions within Entra ID significantly reduced IT overhead, enabling the automation of user onboarding and offboarding processes. This strategic shift allows IT resources to focus on enhancing business processes rather than spending time on account and environment maintenance.
My client’s transformative journey highlights the power of advanced IT solutions and strategic partnerships in modern business environments. Their commitment to providing a seamless user experience serves as an exemplary model for organizations seeking to optimize their collaboration environment. In my next blog, I will share some technical gotchas and lessons learned from the integration work!
