Avoiding Cyber Attacks for your Healthcare Organization
The healthcare industry has always been a high target for cybercriminals. Due to the Covid-19 pandemic, the healthcare industry has had a steady increase in reported cyber-related crime. Financial firms have flagged nearly $600 million in suspected ransomware payments, but the US Treasury identified billions more. The top 10 hacker groups are tied to $5.2 billion in transactions via crypto transactions. According to the US Treasury Department, payouts in 2021 could top the entire past decade.
However, hospital threat actors are not always financially motivated. Hospitals face nation-state actors, internal threats, supply chain threats, opportunist hackers, and much more.
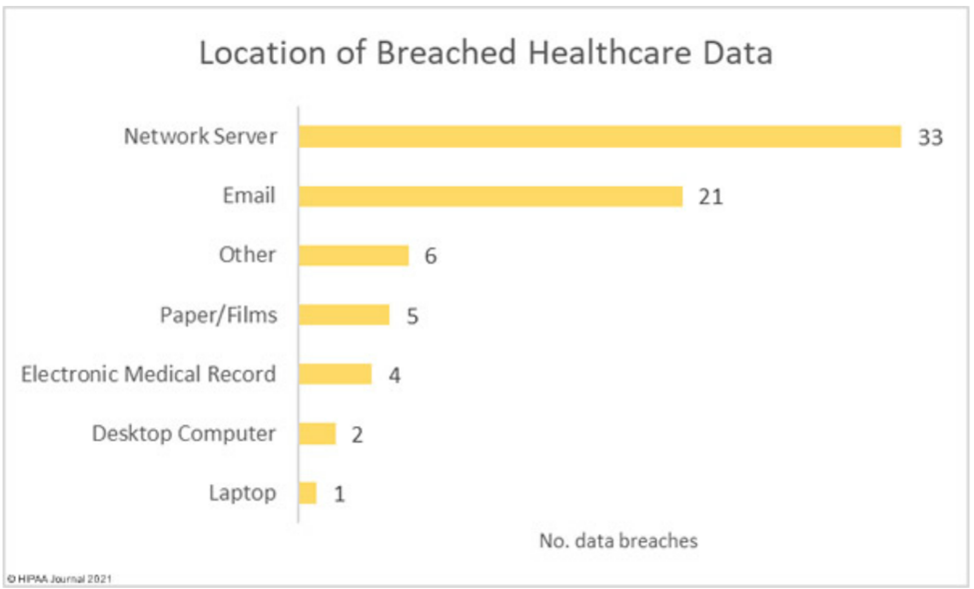
According to the HIPAA Journal, there has been a steady increase in healthcare data breaches. From August 2020 to July 2021, there were 706 reported healthcare data breaches. These have led to the exposure of 44,369,781 individuals.
The largest reported data breach was in July 2021 from a healthcare organization in Wisconsin. This breach compromised 2.4 million individuals. The second-largest data breach reported was a HIPPA healthcare organization from New York. This breach compromised 2.2 million individuals.
Most of the breaches are targeted financially motivated ransomware attacks. With this type of attack, the attackers require their victims to pay a large money ransom to release the data back to the victim or promise not to sell or leak the information.
Many times, cybercriminals target your patients’ Personal Health Information (PHI) and Personal Identifiable Information (PII). This information can have high payouts for cybercriminals on the black market.
The inflation of ransomware attacks has resulted in the National Institute of Standards and Technology (NIST) and the Cyber and Infrastructure Agency (CISA) updating their guidelines on protecting against these types of attacks.
How Do You Keep Your Healthcare Organization Safe?
Many cyberattacks are preventable. Along with encouraging a heightened state of awareness, both NIST and CISA recommend organizations adopt a resiliency strategy. Resilience strategies are used to maintain service levels to critical processes and reduce the risk of system failures.
Additional recommendations on protecting against these attacks include the following Cybersecurity Framework functions:
The Identify function includes developing a structure to understand your organization’s cybersecurity risk to systems, assets, data and capabilities.
Protect –The Protect function empowers your organization to protect itself proactively by developing safeguards to ensure critical infrastructure services are not interrupted during a cyber event. Many organizations use the following to protect their company and data: Cyber Awareness staff training, Identity Access Management control adoption and protective technology such as antivirus and endpoint protection.

Detect – The Detect function ensures proper activities for rapid cyber event detection. This is critical to your cyber program. The faster you can detect a cybersecurity event, the quicker you can respond to mitigate its effects.
Respond – Response planning, communications, analysis, mitigation and improvements are key areas in the Respond function. You need all of these to take effective action during a cyber event. Having an Incident Response Plan (IRP), Business Continuity Plan (BCP) and Disaster Recovery Plan (DRP) will assist in mitigating the incident. Having a plan will help your organization spring into action during a cyber emergency. Some of the steps you can include in your DRP are:
- When you should shut down your network. This will stop the infection from spreading.
- When you should shut down Wi-Fi and Bluetooth.
- Alerting of authorities.
- Regulatory requirements.
- Restore infected files from your backups. If you do not have backups, you may have to submit to the ransom to recover your files, but there is no guarantee you will regain access to all data.
Recover – The Recover function includes recovery planning, improvements and organizational communications. This function is not only important to your organization to recover from an attack, but it is also important to your patients.
Cyberattacks are the fastest growing crime in the United States. They are increasing in size, sophistication and cost. There is no guarantee that even with the best precautions you will prevent this, but the best defense against cybersecurity attacks starts with a solid cyber security plan.
Finally, even operating under the best-protected networks, systems and data protection – cyber impacts will happen. If you have not done so already, consider having a reputable organization with a team of experts that not only understand cyber; but also utterly understands your industry and business beyond the bits and bytes to conduct a Business Impact Assessment (BIA). Every organization has limited resources. BIA is critical for aligning appropriate resources to address threats to your environment and to maximize your organization’s return on mitigation. It is essential in making well-informed decisions prior to the inevitable impacts from occurring.